Trusted Internet Service 633083499 is described as a secure, reliable access solution with programmable controls and user autonomy. Behind the scenes, traffic is encrypted, policy engines enforce rules, and workloads are balanced across trusted nodes. Telemetry supports real-time auditing, and redundancy aims for predictable performance. Trade-offs exist in data use and privacy. The discussion weighs myths against verifiable realities to assess suitability for those who value transparency, leaving the question open for what comes next.
What Is Trusted Internet Service 633083499?
Trusted Internet Service 633083499 refers to a specific, identified online service designed to provide secure, reliable internet access and related management features. The description remains neutral and factual, outlining core purposes and offerings without speculative detail. It emphasizes user autonomy and programmable controls, enabling flexible use. The piece mentions a trusted internet service 633083499 and highlights a behind the scenes discussion for context.
How Does 633083499 Work Behind the Scenes
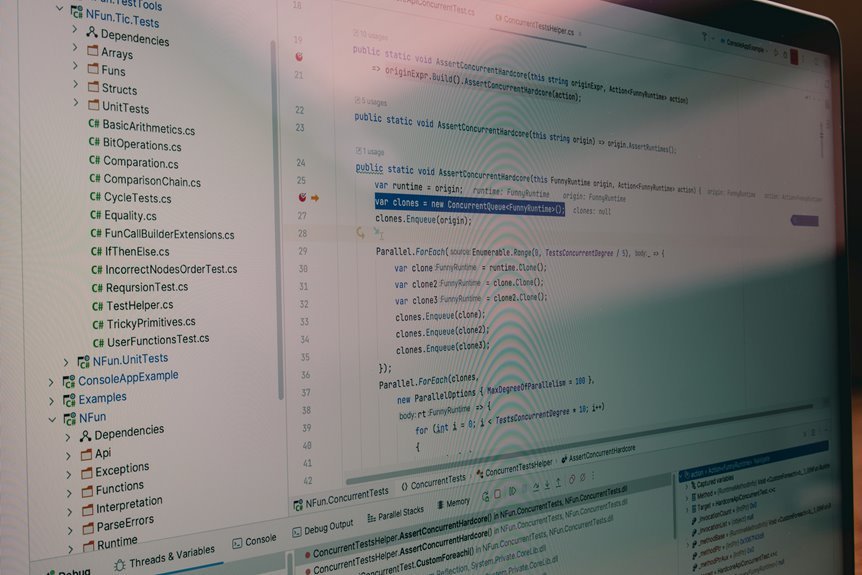
How does 633083499 operate behind the scenes to deliver secure internet access and management features?
Behind the scenes, architectures route traffic through encrypted tunnels, apply policy engines, and balance workloads across trusted nodes.
Access control enforces compliance, while telemetry supports real-time auditing.
Privacy safeguards and data handling protocols minimize exposure, ensuring resilience without compromising user autonomy or performance.
Benefits and Trade-Offs for Privacy, Reliability, and Access
The benefits and trade-offs associated with trusted internet service revolve around balancing privacy, reliability, and access.
The analysis highlights trusted internet advantages, including resilience and predictable performance, while acknowledging privacy tradeoffs and data-use implications.
Reliability benefits emerge from redundancy and failover, yet may impose scrutiny.
Access considerations emphasize equitable availability, geographic reach, and user autonomy, guiding informed, freedom-minded choices.
Debunking Myths and Evaluating Suitability
Evaluating the suitability of a trusted internet service requires separating common myths from verifiable realities and assessing fit against user needs and constraints.
The analysis focuses on debunking myths, scrutinizing unverified claims, and identifying potential biases.
Conclusion
In a quiet harbor, the Trusted Internet Service 633083499 stands as a lighthouse with programmable beams. It guides ships—data packets—through predictable currents, keeping storms at bay with policy-driven tides and encrypted lanterns. Yet its glow requires trustworthy mirrors (privacy trade-offs) and steady, redundant keepers (reliability). For travelers who prize clarity and control, the beacon offers safe passage; for wanderers seeking unguarded horizons, its light may feel confining. The harbor is safer, not free, as promised.